strongSwan VPN Client
An easy to use IKEv2/IPsec-based VPN client.
Version: 2.5.5
Added: 21-08-2021
Updated: 09-04-2025
Added: 21-08-2021
Updated: 09-04-2025
Official Android port of the popular strongSwan VPN solution.
# FEATURES AND LIMITATIONS #
Details and a changelog can be found in our documentation: https://docs.strongswan.org/docs/latest/os/androidVpnClient.html
# PERMISSIONS #
# EXAMPLE SERVER CONFIGURATION #
Example server configurations may be found in our documentation: https://docs.strongswan.org/docs/latest/os/androidVpnClient.html#_server_configuration
Please note that the host name (or IP address) configured with a VPN profile in the app *must be* contained in the server certificate as subjectAltName extension.
# FEEDBACK #
Please post bug reports and feature requests via GitHub: https://github.com/strongswan/strongswan/issues/new/choose
If you do so, please include information about your device (manufacturer, model, OS version etc.).
The log file written by the key exchange service can be sent directly from within the application.


# FEATURES AND LIMITATIONS #
- Uses the VpnService API featured by Android 4+. Devices by some manufacturers seem to lack support for this - strongSwan VPN Client won't work on these devices!
- Uses the IKEv2 key exchange protocol (IKEv1 is not supported)
- Uses IPsec for data traffic (L2TP is not supported)
- Full support for changed connectivity and mobility through MOBIKE (or reauthentication)
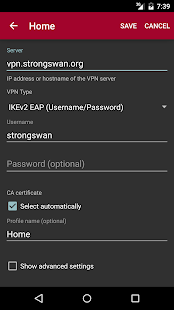
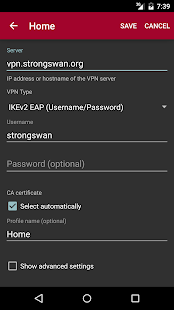
- Supports username/password EAP authentication (namely EAP-MSCHAPv2, EAP-MD5 and EAP-GTC) as well as RSA/ECDSA private key/certificate authentication to authenticate users, EAP-TLS with client certificates is also supported
- Combined RSA/ECDSA and EAP authentication is supported by using two authentication rounds as defined in RFC 4739
- VPN server certificates are verified against the CA certificates pre-installed or installed by the user on the system. The CA or server certificates used to authenticate the server can also be imported directly into the app.
- IKEv2 fragmentation is supported if the VPN server supports it (strongSwan does so since 5.2.1)
- Split-tunneling allows sending only certain traffic through the VPN and/or excluding specific traffic from it
- Per-app VPN allows limiting the VPN connection to specific apps, or exclude them from using it
- The IPsec implementation currently supports the AES-CBC, AES-GCM, ChaCha20/Poly1305 and SHA1/SHA2 algorithms
- Passwords are currently stored as cleartext in the database (only if stored with a profile)
- VPN profiles may be imported from files
- Supports managed configurations via enterprise mobility management (EMM)
Details and a changelog can be found in our documentation: https://docs.strongswan.org/docs/latest/os/androidVpnClient.html
# PERMISSIONS #
- READ_EXTERNAL_STORAGE: Allows importing VPN profiles and CA certificates from external storage on some Android versions
- QUERY_ALL_PACKAGES: Required on Android 11+ to select apps to ex-/include in VPN profiles and the optional EAP-TNC use case
# EXAMPLE SERVER CONFIGURATION #
Example server configurations may be found in our documentation: https://docs.strongswan.org/docs/latest/os/androidVpnClient.html#_server_configuration
Please note that the host name (or IP address) configured with a VPN profile in the app *must be* contained in the server certificate as subjectAltName extension.
# FEEDBACK #
Please post bug reports and feature requests via GitHub: https://github.com/strongswan/strongswan/issues/new/choose
If you do so, please include information about your device (manufacturer, model, OS version etc.).
The log file written by the key exchange service can be sent directly from within the application.